Your IP address is a digital fingerprint, a unique identifier that marks your presence on the internet. Understanding what it is and why it matters ….
Cybercriminals pose a constant threat to personal and organisational data. This article explores common hacking methods and offers strategies to protect yourself and your information. ….
Email attachments are a fundamental component of digital communication. They allow for the efficient transfer of files and documents. However, this convenience carries inherent risks. ….
Cybersecurity is the practice of protecting systems, networks, and programmes from digital attacks. Cyberattacks typically aim to access, alter, or destroy sensitive information, extract money ….
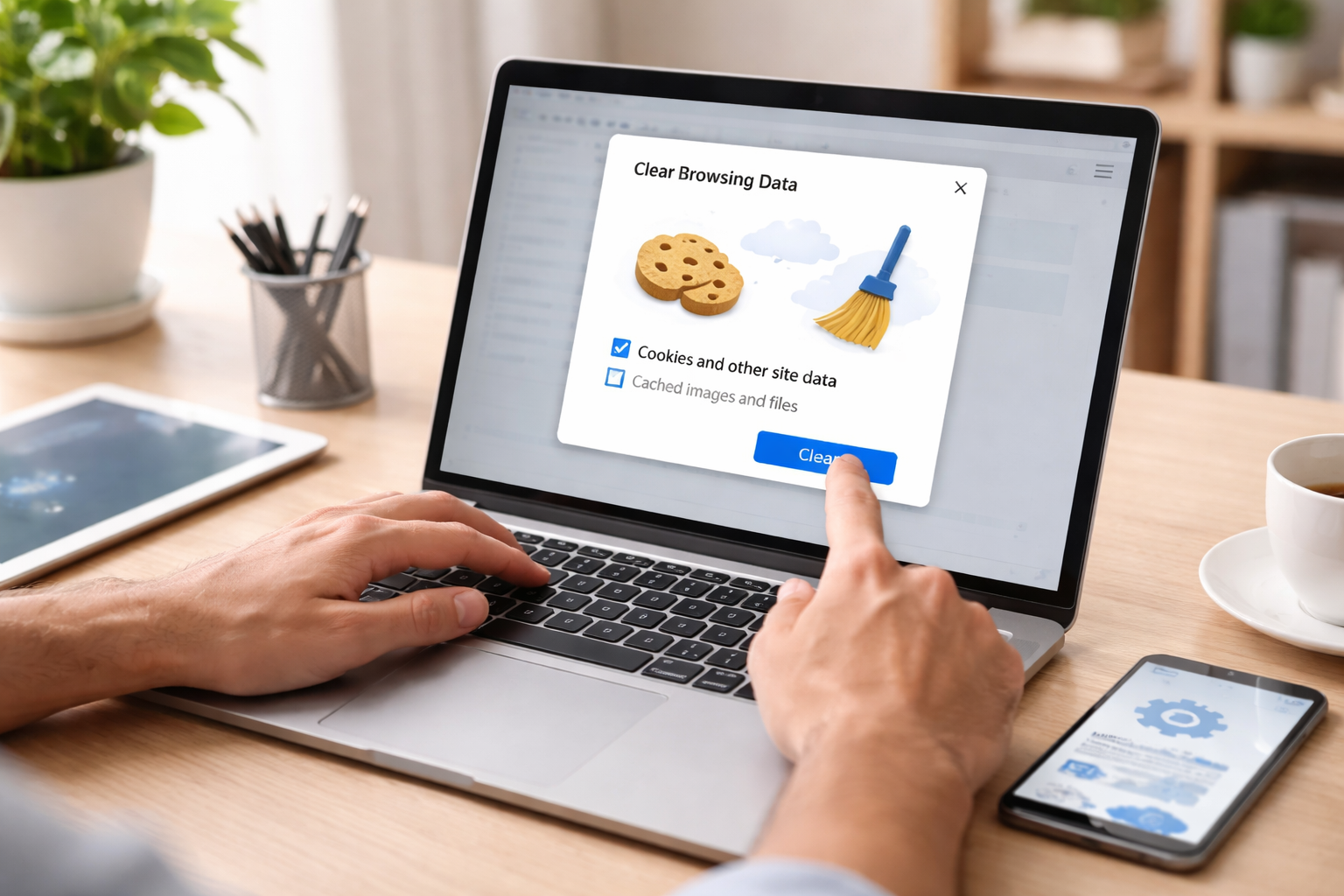
Your device, whether a computer, tablet, or smartphone, constantly works to deliver information quickly. To achieve this, it uses temporary storage spaces, much like a ….
A Virtual Private Network (VPN) creates a secure connection over a less secure network. Imagine sending a sealed letter through the public postal service. The ….
Resetting a router can resolve many common internet connectivity problems. This guide provides clear instructions and explanations. A router acts as the traffic director for ….
Software errors are an inherent part of the development and operation of any software system. They range from minor glitches that cause inconvenience to critical ….
Online privacy is essential in the digital age. It refers to the level of privacy protection an individual has while connected to the internet. This ….
The security of Internet of Things (IoT) devices is a growing concern for individuals and organizations alike. These devices, ranging from smart thermostats and security ….