Windows, as a widely used operating system, can encounter various issues. This guide provides a systematic approach to troubleshooting common problems, offering solutions to restore ….
Driver updates are essential software revisions that improve how your computer’s hardware interacts with its operating system. These small programs act as translators, allowing components ….
This article covers methods for protecting a Mac from malware. It discusses the current landscape of Mac malware, best practices for prevention, essential security software, ….
In the digital age, data is a valuable asset, and protecting it is paramount. Cybersecurity tools are the digital guardians that defend networks, systems, and ….
Online banking offers convenience, allowing users to manage their finances from virtually anywhere. However, this accessibility creates opportunities for those who wish to exploit vulnerabilities ….
Online scams are a persistent threat, and understanding how to identify and avoid them is crucial for safe internet use. Scam websites are designed to ….
Cyber threats constantly evolve, creating a dynamic challenge for security professionals and the public alike. From straightforward phishing attempts to sophisticated fileless malware, understanding these ….
Small businesses, like larger enterprises, face a growing array of cybersecurity threats. While often perceived as less attractive targets than corporations, their limited in-house security ….
In this era of easy information sharing and widespread access, safeguarding digital documents is crucial. This article offers guidance on securing sensitive information within Portable ….
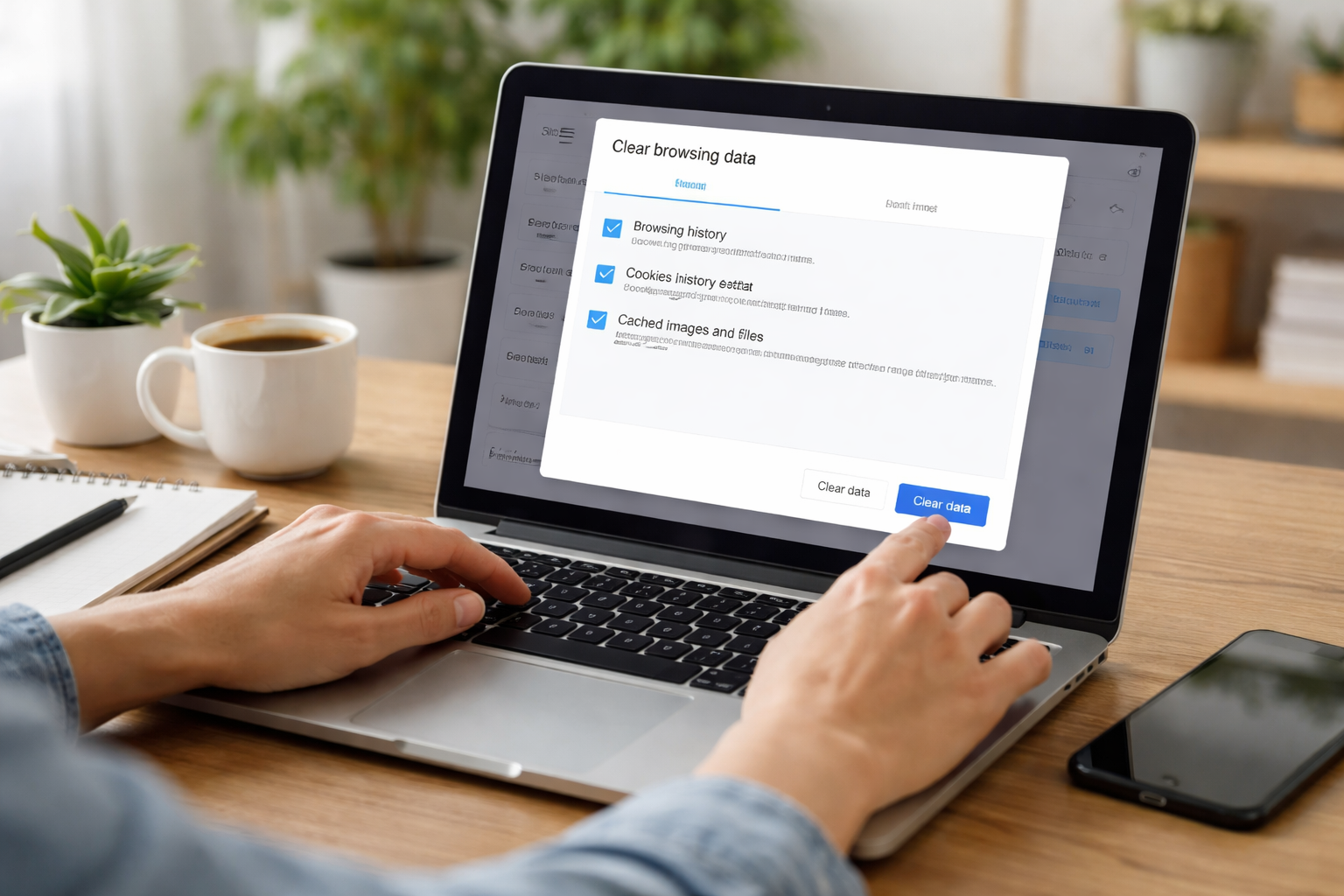
Clearing your browsing history is a fundamental practice for maintaining digital privacy and security. Your browsing history acts as a digital trail, documenting your activities ….