Router resetting is a common procedure for resolving network connectivity issues. This article aims to provide a practical guide to understanding, performing, and benefiting from ….
Author: admin
The internet offers convenience, but it also presents risks. Understanding these dangers and implementing protective measures is essential for safe online shopping. This guide addresses ….
The internet, a vast digital ocean, offers unparalleled access to information and connection. However, this interconnectedness also presents challenges to personal privacy. Understanding how your ….
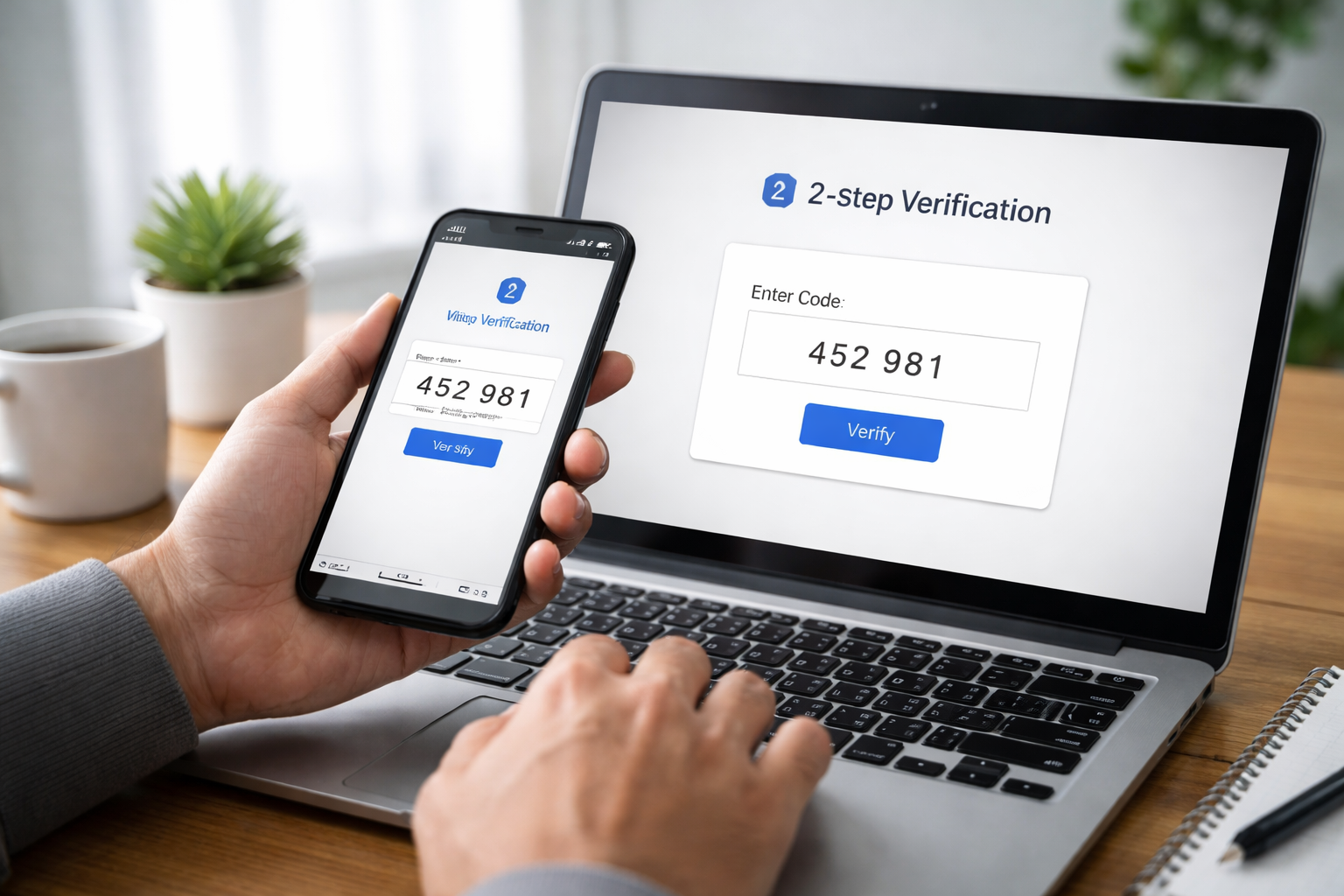
The need for strong online security is a constant battle. As more of our lives move online, from banking to social connections, the potential for ….
Virtual Private Networks (VPNs) have become integral tools for navigating the modern internet. Their core function, creating a secure tunnel for online traffic, has expanded ….
“Malware,” a portmanteau of “malicious software,” refers to any software designed to disrupt computer operations, gather sensitive information, or gain unauthorised access to computer systems. ….
Online meetings have become a cornerstone of modern communication, facilitating collaboration and connection across distances. However, their widespread use also presents security challenges. This guide ….
Phishing is a type of online fraud where criminals attempt to trick individuals into revealing sensitive information, such as usernames, passwords, credit card details, or ….
Privacy protection in the digital age requires a multi-layered approach, and technological advancements offer various tools to enhance personal and professional security. This article explores ….
Cloud storage offers convenience and accessibility, but it also introduces security challenges. Understanding these challenges and implementing appropriate safeguards is crucial for protecting your digital ….